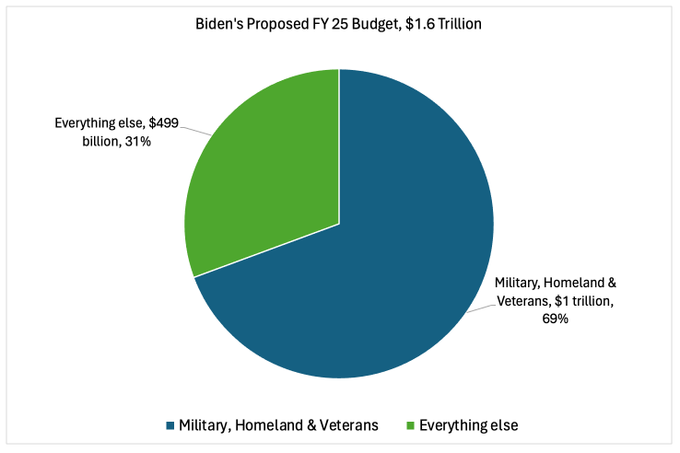
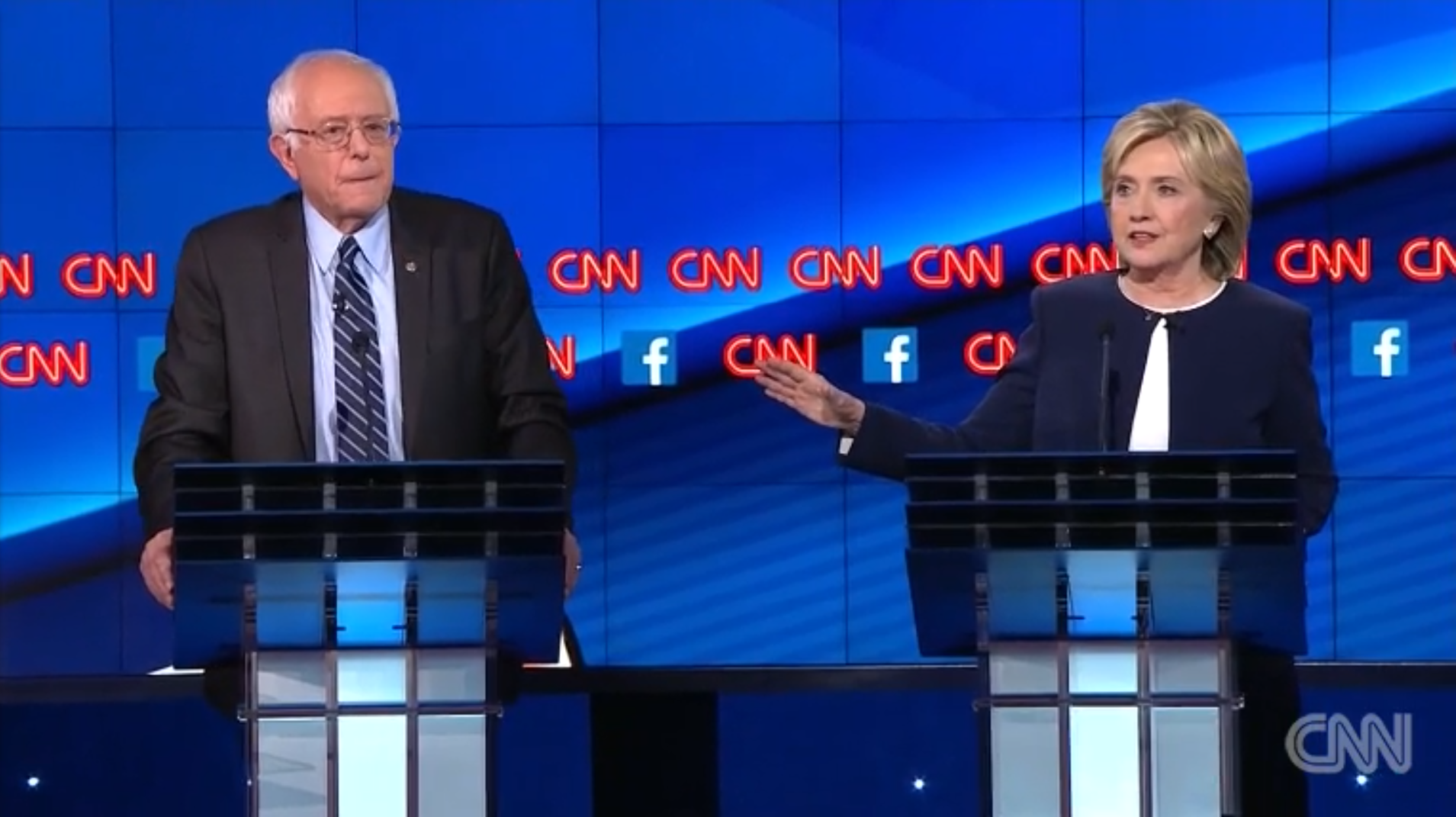
Militarized Funding in Biden Budget Totals Well Over $1 Trillion (and it will grow)
Unless the administration changes its approach, these wars will continue to deprive us of the security we actually need.
Unless the administration changes its approach, these wars will continue to deprive us of the security we actually need.

New resource explains how over-investment in militarism and under-investment in climate solutions have contributed to the failure to mitigate climate change – and that ways that we can reinvest military spending to combat the worst existential threat to our communities.

How Washington’s climate spending compares to its investments in the military.

In The Nation, Bill Hartung reviews IPS Associate Fellow Miriam Pemberton’s new book.

As we saw in Texas, climate change is a major security risk. But it’s not the kind the military is well equipped to handle.

Militarism isn’t security. Real security encompasses justice, health, housing, food, education, and civil rights.

In this interview with Vox, IPS drug policy expert Sanho Tree explains how evolution could have predicted the failure of the war on drugs.
No matter how tall or deep Trump’s wall is, it will not stop the flow of drugs or traffickers into the U.S., in fact it will heighten the national security risk.

Should we rethink the way voters weigh in directly on matters of national security and international relations?

Help us spread the word about our latest report, “Combat Vs. Climate: The Military and Climate Security Budgets Compared”

The Military and Climate Security Budgets Compared

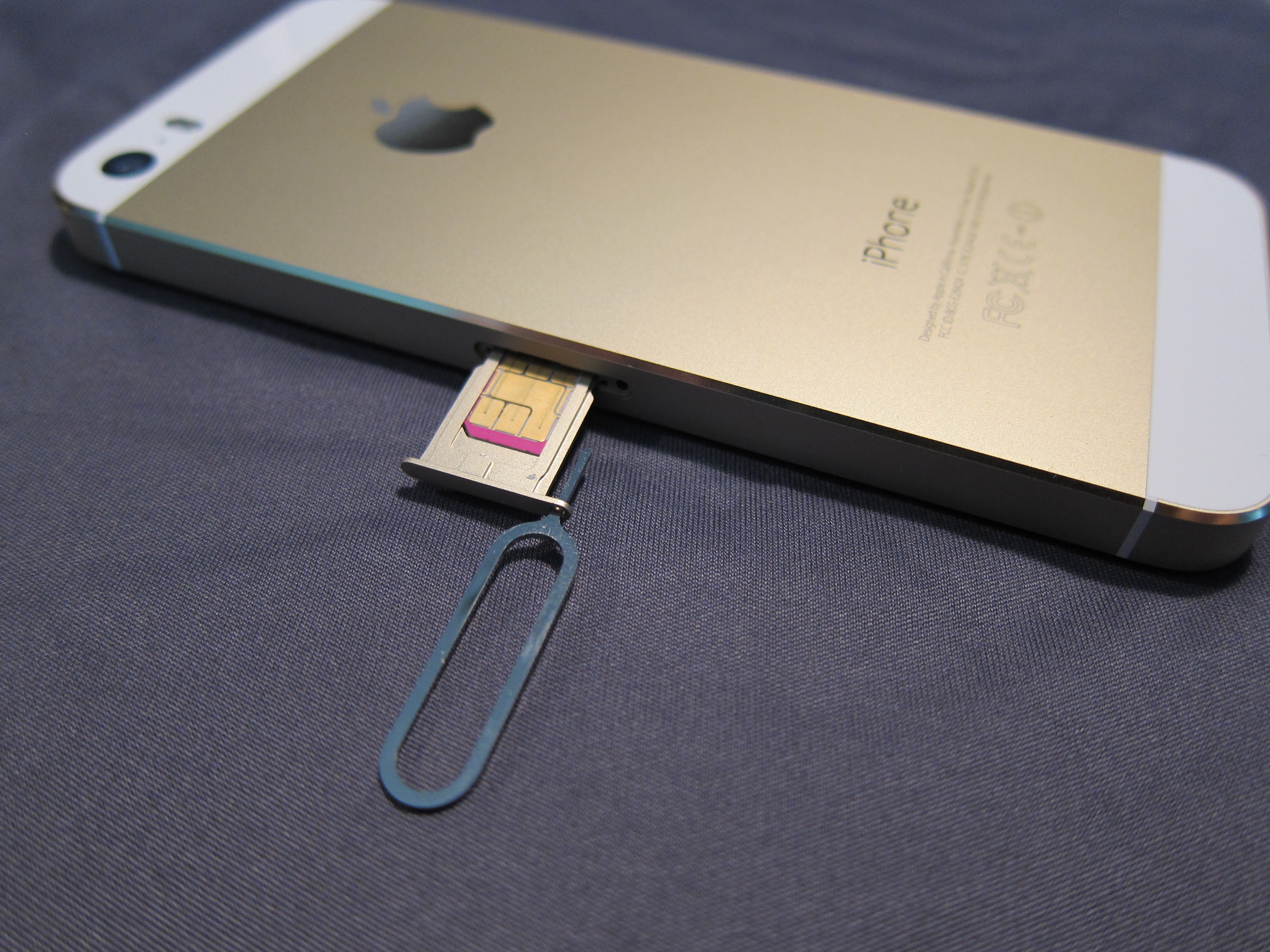
IPS’s Phyllis Bennis tells the Real News Network that although Clinton rightfully used her national security speech to condemn the bigotry and danger of Trump’s positions, she didn’t lay out a much better alternative.
The feds dropped the ball on a key terrorism case, so now they’re going after privacy itself.
In a field defined more by conformity than contradiction, here’s where the candidates split.
A new special issue of The Nation brings an inequality frame to our current cyber world.